Anatomy of a Modern Data Leak How AI Connects the Dots That Rules Can’t See
A public URL, a Slack thread, and one message to a former employee—how contextual analysis revealed a pre-IPO acquisition leak traditional tools missed.

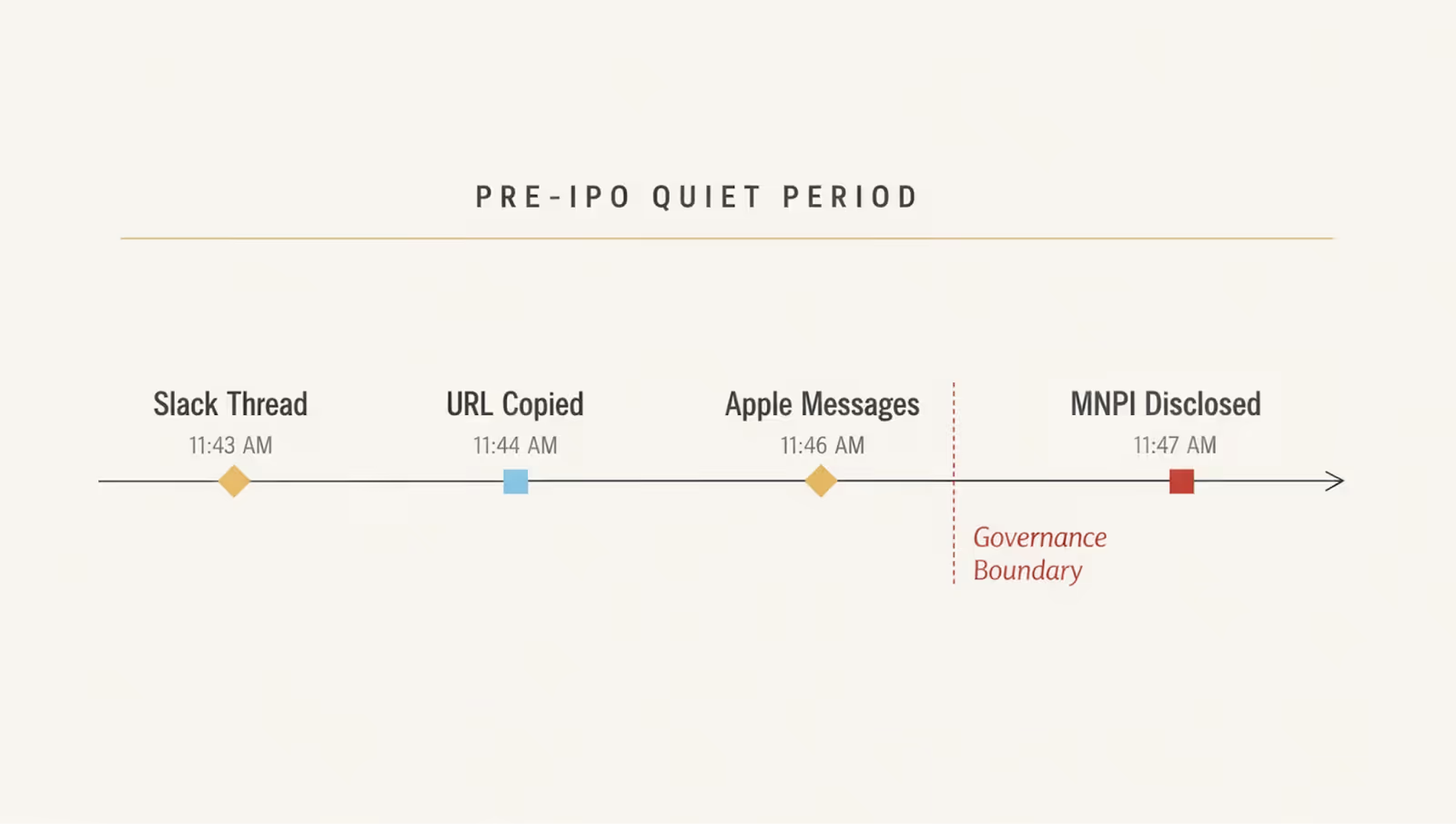
At 11:43 AM, a message appeared in a private Slack channel.
The channel name included the words “final approval.”
The discussion was about an acquisition that had just been internally confirmed.
The acquisition wasn’t public. The company was weeks away from an IPO.
At 11:44 AM, an employee copied a URL from that Slack thread.
The URL itself was public. Just a normal website.
Nothing sensitive in isolation.
At 11:46 AM, that URL was sent through Apple Messages to an external contact — a former employee.
At 11:47 AM, he added:
“Don’t tell anyone, but this is the company we’re acquiring.”
No confidential attachment. No spreadsheet. No obvious policy keyword.
The leak was just a URL, and context.
Why Nothing Traditional Would Have Caught It
If you isolate each piece, nothing looks dangerous.
A public URL.
A Slack copy event.
A message sent via Apple Messages.
An employee in business development.
A traditional DLP engine inspects the string — no match.
A CASB sees outbound communication — but not meaning.
A DSPM tool sees no sensitive file accessed at rest.
There is no clear policy violation - because rules operate on fragments. And this leak only exists when you reconstruct the sequence.
No regex pattern in the world captures materiality.
This Wasn’t “Oversharing”
In a pre-IPO environment, timing is everything. Premature disclosure of an acquisition can:
• Trigger insider trading scrutiny
• Raise SEC compliance exposure
• Impact valuation
• Undermine deal negotiations
This wasn’t about a URL leaving Slack. It was about material non-public information leaving the organization at exactly the wrong moment.
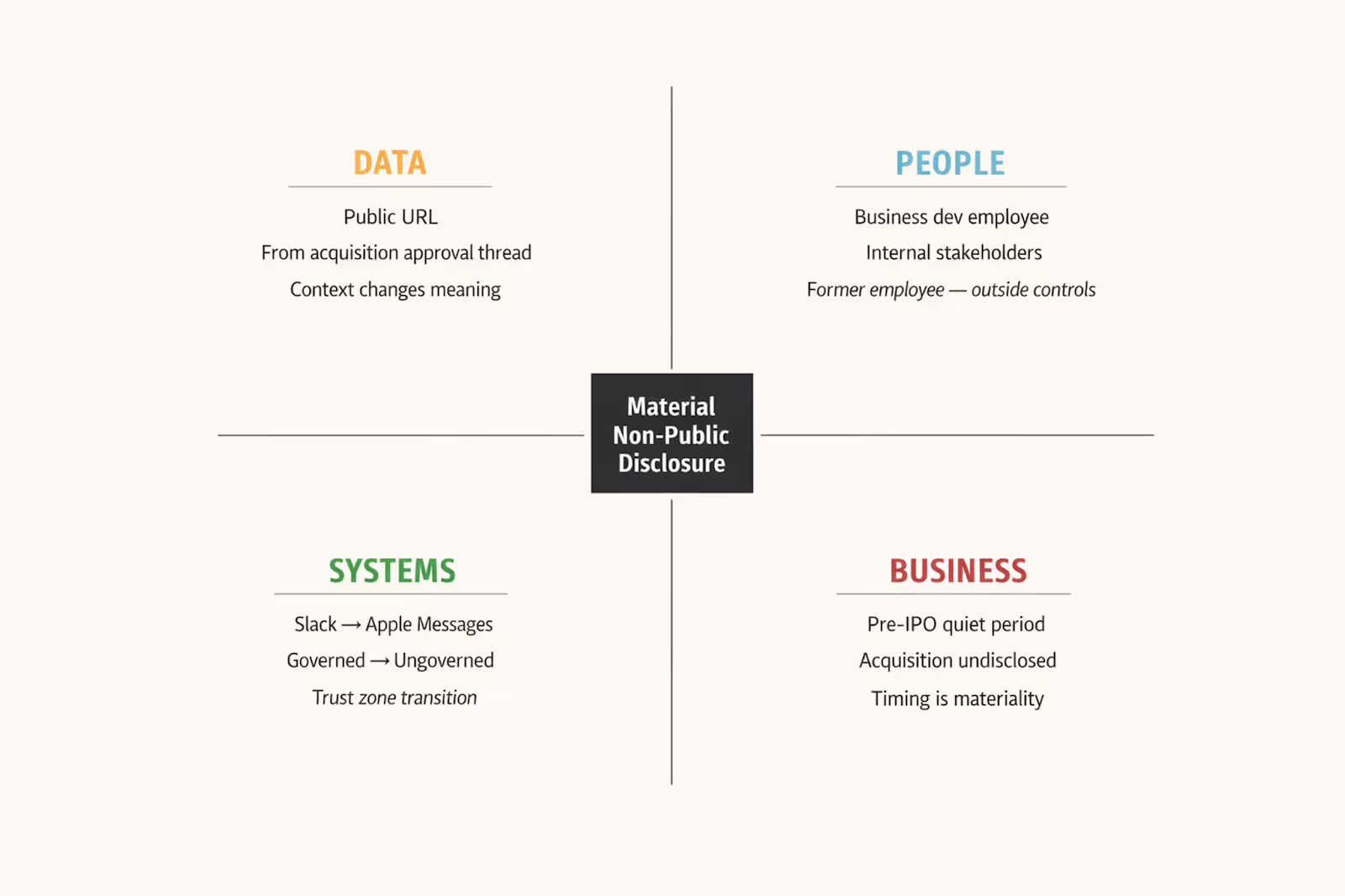
Looking at the Same Moment Through Four Lenses
What made this leak visible to Jazz’s Agentic Investigator, Melody, was perspective. To understand why this mattered, you have to look at the event through four lenses at once:
Data. People. Systems. Business.
Data
Yes, it was a public URL. But it was copied from a Slack thread tied to finalized acquisition approval.
In that context, it wasn’t “just a website.” It was a pointer to non-public M&A intelligence. Data changes meaning depending on where it comes from.
People
This wasn’t simply “an employee messaging someone external.” It involved three identity layers:
• 1st party — A business development employee with legitimate access
• 2nd party — Internal stakeholders participating in a confidential event
• 3rd party — A former employee, outside corporate controls but fully aware of what this implied
He wasn’t malicious, but he crossed a boundary. And in data security, boundaries matter.
Systems
The path was:
Slack → copy → Apple Messages.
Slack was governed, Apple Messages was not. Neither system is inherently risky, but transitions between trust zones are where exposure happens.
Business
The organization was preparing for an IPO, and the acquisition was not public. Disclosure timing was critical.
In another month, that same message might have been harmless. At that moment, it was market-moving. The risk didn’t live in any single pillar, but rather in their intersection.
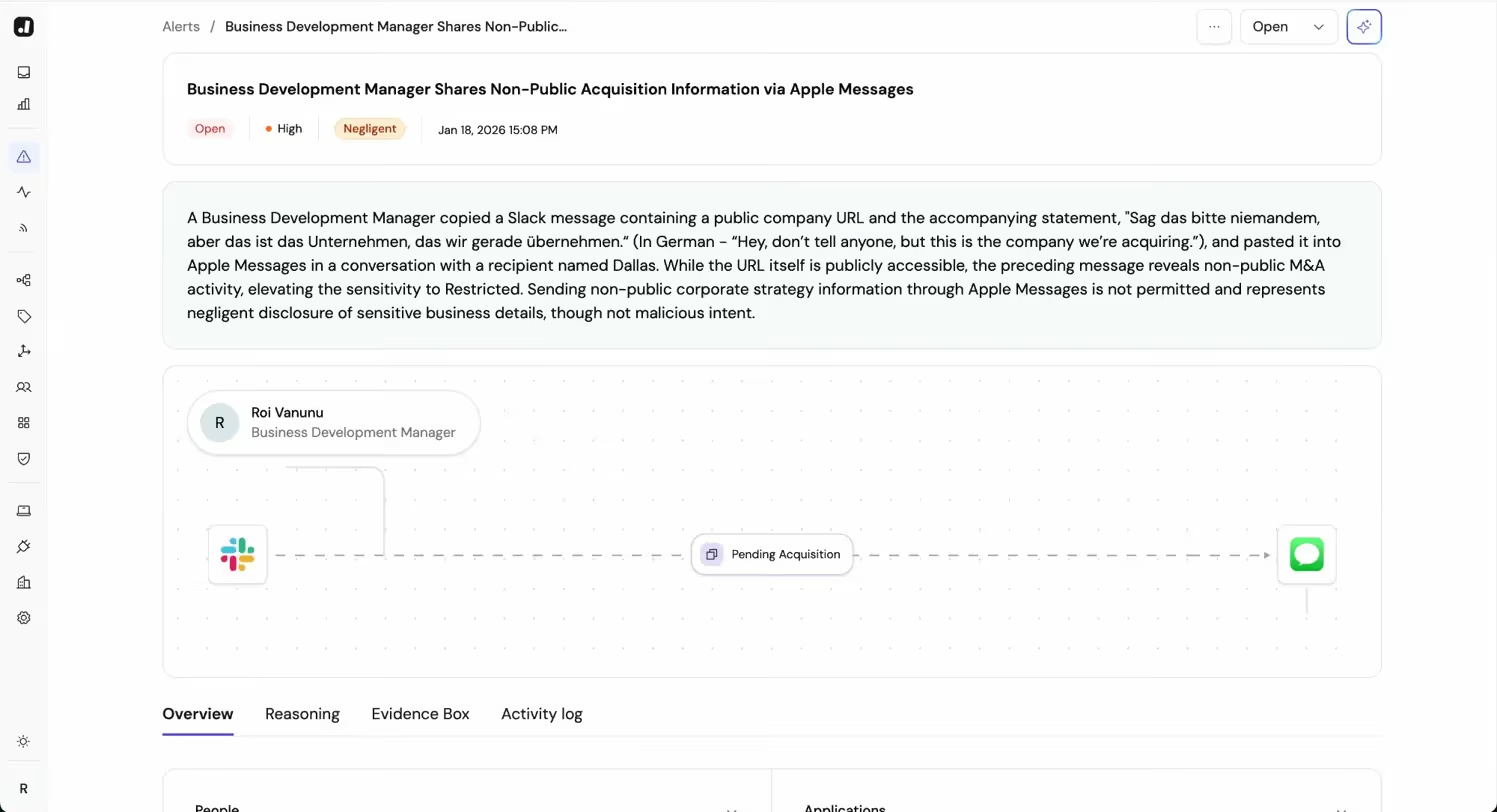
When the Fragments Become a Story
Individually, each lens sees something explainable. But together, they reveal something else.
The reconstructed narrative looked like this:
“Business development employee
Copies URL from acquisition approval thread
Sends it to former employee
During pre-IPO quiet period
Explicitly confirms acquisition”
That’s not a keyword match - that’s a story. And modern leaks hide inside stories.
How Melody Connects the Dots
Under the hood, this reconstruction isn’t manual. Each of those lenses is continuously evaluated by a dedicated reasoning agent.
One agent understands data provenance.
One understands identity relationships and boundaries.
One understands system transitions and trust zones.
One understands business context and materiality.
Each agent produces structured findings, and those findings are reconciled into a full story, explainable narrative.
And this reasoning isn’t stateless. Melody maintains organizational memory:
• Which initiatives are restricted
• Which partners are sanctioned
• Where identity boundaries exist
• What prior investigations established as acceptable
When the recipient was identified as a former employee, that mattered because the system already understood the boundary between current and former insiders.
When the business context was evaluated, it mattered because the IPO state was part of persistent knowledge. This was the result of deep contextual understanding only humans could’ve achieved - until now.
